- Home
-
My Work
- Cyber Security Fundamentals
- Cryptography
- Security Architecture
- Operational Policy
- Risk Management
- Management and Cyber Security
- Secure Software Design and Development
- Network Visualization and Vulnerability Detection
- Cyber Threat Intelligence
- Incident Response and Computer Network Forensics
- Capstone
- Contact
- Reference Link Library
Introduction
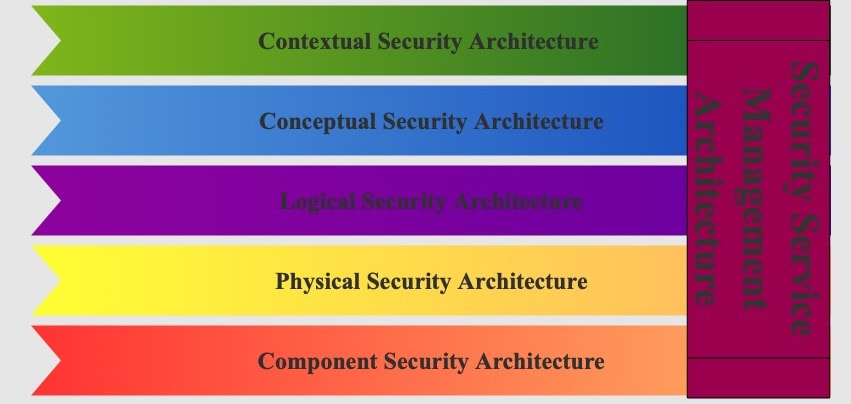
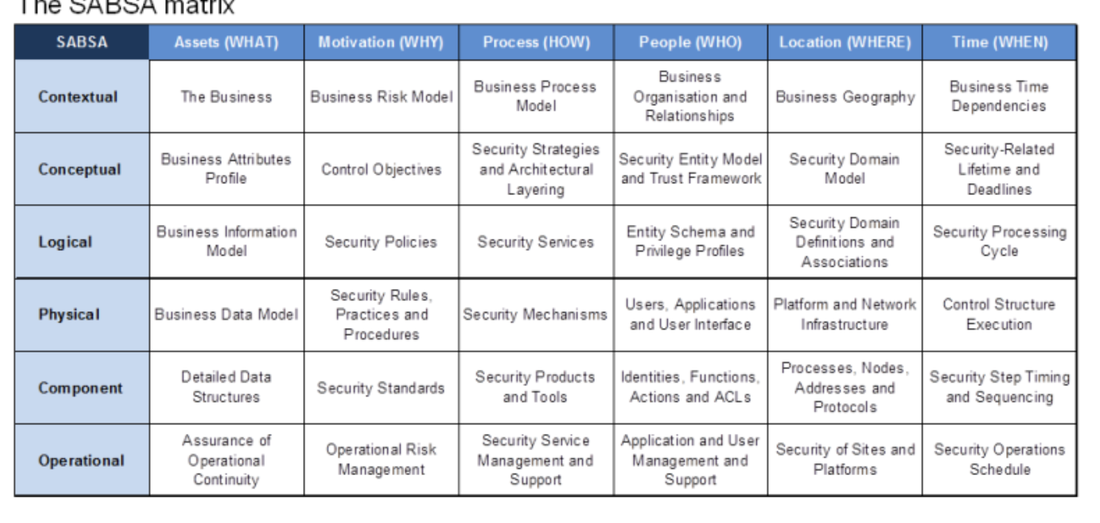
Security architecture is a method organizations use to design and implement secure systems. It comprises 6 layers: contextual, conceptual, logical, physical, component, and operational (management). The Sherwood Applied Business Security Architecture (SABSA) model is heavily used by organizations when planning their security architecture. It is constructed from the top to down hierarchy and builds off each other. Therefore, skipping a layer will have critical information missing. Some may see this as a positive design due to overcoming challenges on the spot. Some may see this as a negative design because they can not skip and come back to it when time permits.
Each layer addresses the Who, What, Where, When, Why, and How (5 Ws & H) questions separately. When first learning about security architecture, this may be confusing, but it gets easier once you break it down separately.
The beauty of the SABSA is the 36-cell matrix. The 6 layers are crossed with the 5 W’s & H to help organize the information.
The beauty of the SABSA is the 36-cell matrix. The 6 layers are crossed with the 5 W’s & H to help organize the information.
Contextual Security Architecture (Business View)
The first layer of the SABSA model and the most crucial. This layer defines the business requirements and sets the foundation for the other layers. We address the 5W’s & H to understand the business requirements clearly.
Questions to answer concerning Contextual Architecture
Assets (What): Business Decisions
Motivation (Why): Business Risk
Process (How): Business Processes
People (Who): Business Governance
Location (Where): Business Geography
Time (When): Business Time Dependence
Questions to answer concerning Contextual Architecture
Assets (What): Business Decisions
Motivation (Why): Business Risk
Process (How): Business Processes
People (Who): Business Governance
Location (Where): Business Geography
Time (When): Business Time Dependence
Conceptual Security Architecture (Architect’s View)
The conceptual layer is known as the architect's view because it starts to put together the requirements from the contextual layer. This layer is the 10,000-foot view to protect the system. Building this layer sets the pace for the following two layers when it starts to be planned.
Questions to answer concerning Conceptual Architecture
Assets (What): Business Knowledge & Risk Strategy
Motivation (Why): Risk Management Objectives
Process (How): Strategies for Process Assurance
People (Who): Roles & Responsibilities
Location (Where): Domain Framework
Time (When): Time Management Framework
Questions to answer concerning Conceptual Architecture
Assets (What): Business Knowledge & Risk Strategy
Motivation (Why): Risk Management Objectives
Process (How): Strategies for Process Assurance
People (Who): Roles & Responsibilities
Location (Where): Domain Framework
Time (When): Time Management Framework
Logical Security Architecture (Designer’s View)
The designer interprets the architect's vision in the previous layer and implements a logical structure. The designer will implement security policies, services, domains, and other logical abstractions.
Questions to answer concerning Logical Architecture
Assets (What): Information Assets
Motivation (Why): Risk Management Policies
Process (How): Process Maps & Services
People (Who): Entity & Trust Framework
Location (Where): Domain Maps
Time (When): Calendar & Timetable
Questions to answer concerning Logical Architecture
Assets (What): Information Assets
Motivation (Why): Risk Management Policies
Process (How): Process Maps & Services
People (Who): Entity & Trust Framework
Location (Where): Domain Maps
Time (When): Calendar & Timetable
Physical Security Architecture (Builder’s View)
The builder produces the logical structure into a physical security architecture. This layer describes the technology model used to meet all the requirements from the designer’s view. This layer takes a deep dive into the security architecture because security mechanisms, access control, encryption, backups, and recovery are defined and developed in this layer.
Questions to answer concerning Physical Architecture
Assets (What): Data Assets
Motivation (Why): Risk Management Practices
Process (How): Process Mechanisms
People (Who): Human Interface
Location (Where): ICT Infrastructure
Time (When): Processing Schedule
Questions to answer concerning Physical Architecture
Assets (What): Data Assets
Motivation (Why): Risk Management Practices
Process (How): Process Mechanisms
People (Who): Human Interface
Location (Where): ICT Infrastructure
Time (When): Processing Schedule
Component Security Architecture (Tradesman’s View)
The tradesman view starts to use all the technology from the previous layers to ensure everything works within expectancy. In this layer, business continuity and operational risk management are constructed.
Questions to answer concerning Component Architecture
Assets (What): ICT Components
Motivation (Why): Risk Management Tools & Standards
Process (How): Process Tools & Standards
People (Who): Personnel Management Tools & Standards
Location (Where): Locator Tools & Standards
Time (When): Step Timing & Sequencing Tools
Questions to answer concerning Component Architecture
Assets (What): ICT Components
Motivation (Why): Risk Management Tools & Standards
Process (How): Process Tools & Standards
People (Who): Personnel Management Tools & Standards
Location (Where): Locator Tools & Standards
Time (When): Step Timing & Sequencing Tools
Operational Security Architecture (Facilities Manager’s View)
This layer puts all the previous layers together and creates a day to day operations. The facility manager ensures the operations are in working order, monitored, and performed as designed.
Questions to answer concerning Management Architecture
Assets (What): Service Delivery Management
Motivation (Why): Operational Risk Management
Process (How): Process Delivery Management
People (Who): Personnel Management
Location (Where): Management of Environment
Time (When): Time & Performance Management
Questions to answer concerning Management Architecture
Assets (What): Service Delivery Management
Motivation (Why): Operational Risk Management
Process (How): Process Delivery Management
People (Who): Personnel Management
Location (Where): Management of Environment
Time (When): Time & Performance Management
Reflection
Learning security architecture was difficult due to the multiple layers and questions that needed to be addressed. As technology advances, we face difficult challenges to overcome in cybersecurity. Utilizing the SABSA matrix, we can prioritize and organize our goals to overcome those challenges. Since the SABSA layers are built off each other, we meet each requirement if we answer every question thoroughly. When reading about breach incidents or data leaks, I wonder how security architecture was designed and implemented. The SABSA model goes into detail on by using the 5 W and H to ensure every area is covered properly.