- Home
-
My Work
- Cyber Security Fundamentals
- Cryptography
- Security Architecture
- Operational Policy
- Risk Management
- Management and Cyber Security
- Secure Software Design and Development
- Network Visualization and Vulnerability Detection
- Cyber Threat Intelligence
- Incident Response and Computer Network Forensics
- Capstone
- Contact
- Reference Link Library
Management and Cyber Security
Information Systems Security Plan (ISSP) is an important cybersecurity strategy because it identifies and describes multiple controls in place for the system. There are three types of controls used when developing an ISSP. Managerial controls focus on the security policies, standard operating procedures, and controls that address security design and implementation. Operational controls are awareness programs, security guards, and controls people implement. Technical controls are implemented using systems, operating systems, firewalls, anti-virus, and other related controls. These controls are used alone or together to protect against risk and vulnerabilities. It is a guideline that we, as cybersecurity professionals, created to address security concerns and requirements.
Disaster Recovery Plan (DRP)
The purpose of a DRP is to create a safety net in case a disaster happens. An example of a disaster can be a natural, cyber attack, or human error. Having a DRP in place will give an organization a sign of relief that they have planned for the worse. DRP can be approached in 4 different ways, depending on how much the organization is willing to spend.
Disaster Recovery as a Service (DRaaS): This service provider will provide a cloud computing environment in case there is a failure in the system.
Cold Site: The organization purchases an infrastructure but lacks equipment or technology. Recovery may take weeks.
Warm Site: The organization purchases an infrastructure with equipment or technology but does not have the data. Recovery may take days/hours.
Hot Site: Fully functional and ready to go in a disaster. Recovery within hours/minutes.
Disaster Recovery as a Service (DRaaS): This service provider will provide a cloud computing environment in case there is a failure in the system.
Cold Site: The organization purchases an infrastructure but lacks equipment or technology. Recovery may take weeks.
Warm Site: The organization purchases an infrastructure with equipment or technology but does not have the data. Recovery may take days/hours.
Hot Site: Fully functional and ready to go in a disaster. Recovery within hours/minutes.
Your browser does not support viewing this document. Click here to download the document.
Return on Investment (ROI)
Cybersecurity is an investment for an organization because it provides protection and prevents future security risks. Although cybersecurity does not actively gain revenue, it reduces the chances of losing assets. The ROI calculation is expressed as the organization (Revenue - Cost) = Profit. The amount of money saved through cybersecurity implementation is described as “Revenue,” and the security control cost is defined as “Cost.” At any time, an organization may suffer from a security breach that is expensive to recover from. Investing in cybersecurity will reduce the chances of a security breach, ultimately preventing future fines and lawsuits.
If a data breach is estimated to be about $2,000 to fix and a system misconfiguration is about $1,000, then we calculate the Annual Loss Expectancy (ALE).
Example:
Annualized Rate of Occurrence (ARO)
Single Loss Expectancy (SLE).
ALE = ARO x SLE
ALE = (5 data breaches) x ($2,000)
ALE = $10,000 (Data Breaches)
ALE = (10 System Misconfigurations) x ($1,000)
ALE = $10,000 (System Misconfigurations)
ALE = $10,000 + $10,000
ALE = $20,000
An organization is spending $20,000 annually due to data breaches and system misconfigurations. Investing in cybersecurity will help reduce this cost by decreasing the ARO and implementing new security controls. Examples of security controls are implementing firewalls, security policies, and segmenting networks. An estimate to place a firewall and security policies is $500. With the new security control in place, it has reduced data breaches and system misconfiguration to 2 times per year.
Example
RIO % = [(RIO - (Cost of Control) / (Cost of Control)] x 100
RIO = (2 data breaches) x ($2,000)
RIO = $4,000
RIO % = [($4,000 - $500) / $500] x 100
RIO % = 700%
RIO = (2 System Misconfigurations) x ($1,000)
RIO = $2,000
RIO % = [($2,000 - $500) / $500] x100
RIO % = 300%
Both Security Control Calculations
RIO % = [( $6,000 - $500) / $500] x 100
RIO % = 1100%
Cybersecurity plays a vital role in complying with multiple laws and regulations. Cybersecurity is an investment toward an organization's future because it reduces risk, meets compliance, and meets business objectives. To minimize risk, security controls can be implemented to strengthen the system and reduce breaches.
If a data breach is estimated to be about $2,000 to fix and a system misconfiguration is about $1,000, then we calculate the Annual Loss Expectancy (ALE).
Example:
Annualized Rate of Occurrence (ARO)
Single Loss Expectancy (SLE).
ALE = ARO x SLE
ALE = (5 data breaches) x ($2,000)
ALE = $10,000 (Data Breaches)
ALE = (10 System Misconfigurations) x ($1,000)
ALE = $10,000 (System Misconfigurations)
ALE = $10,000 + $10,000
ALE = $20,000
An organization is spending $20,000 annually due to data breaches and system misconfigurations. Investing in cybersecurity will help reduce this cost by decreasing the ARO and implementing new security controls. Examples of security controls are implementing firewalls, security policies, and segmenting networks. An estimate to place a firewall and security policies is $500. With the new security control in place, it has reduced data breaches and system misconfiguration to 2 times per year.
Example
RIO % = [(RIO - (Cost of Control) / (Cost of Control)] x 100
RIO = (2 data breaches) x ($2,000)
RIO = $4,000
RIO % = [($4,000 - $500) / $500] x 100
RIO % = 700%
RIO = (2 System Misconfigurations) x ($1,000)
RIO = $2,000
RIO % = [($2,000 - $500) / $500] x100
RIO % = 300%
Both Security Control Calculations
RIO % = [( $6,000 - $500) / $500] x 100
RIO % = 1100%
Cybersecurity plays a vital role in complying with multiple laws and regulations. Cybersecurity is an investment toward an organization's future because it reduces risk, meets compliance, and meets business objectives. To minimize risk, security controls can be implemented to strengthen the system and reduce breaches.
Your browser does not support viewing this document. Click here to download the document.
Cybersecurity Staffing
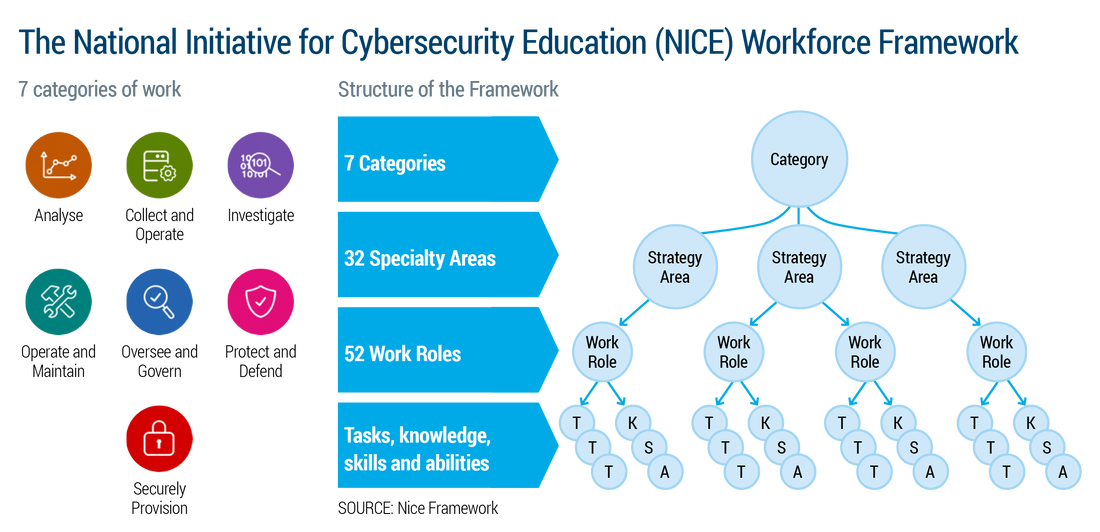
Building a successful cybersecurity team involves knowledge, skills, and abilities (KSAs). Different-level careers require a vast combination of KSAs and characteristics. Additionally, a candidate with certifications, degrees, experience, licenses, or skills comes into consideration, depending on the level they are applying for. The National Institute of Standards and Technology developed the National Initiatives for Cybersecurity Education (NICE) framework highlighting different categories of fields in cybersecurity.
Each category has the sole purpose of meeting all the angles of the cybersecurity industry. Fulfilling each category of the NICE framework will develop a prospering team ready to handle any operation. Once the categories have been filled, the organization can tailor the specialty areas and work roles to meet the organization's needs.
Your browser does not support viewing this document. Click here to download the document.
Reflection
This course was the most beneficial course I have taken in the whole CSOL program because I was able to land my first cybersecurity job with the knowledge I learned during the period. During my interview, the organization asked if I knew what an Information Systems Security Plan (ISSP) was. Immediately I could explain to them what it is and how to develop, implement and maintain one. I explained the security controls in-depth and referred to different NIST publications. I chose these artifacts because, immediately starting the position, I was tasked to create and propose a DRP. When assigned to create a DRP, I knew exactly what to do and what additional questions to ask in advance. As soon as I received the information needed, I was able to create and propose the DRP days before the deadline was due. My boss was impressed with how informed I was on creating a DRP and tasked me to complete more for different programs.
By creating an ISSP, I proposed different security controls and products that can help the organization stay protected. I made a report explaining the Return on Investment (ROI) calculation: (Revenue - Cost) = Profit. I further broke it down to Annual Loss Expectancy (ALE), Annualized Rate of Occurrence (ARO), and Single Loss Expectancy (SLE).
ALE = ARO x SLE.
My report explains that cybersecurity is an investment that does not produce revenue but prevents money from being spent on incidents. Therefore, the saved money would be considered as the revenue in the formula. Being confident in what I learned in this course, I was able to have the organization purchase an Uninterruptable Power Supply (UPS) for multiple critical systems. The UPS will save the organization time and money by not having to restart their work and have time to offload or keep work that has been done. The knowledge I learned during the course I could immediately implement to my job and teach others the importance of a DRP and ISSP.
By creating an ISSP, I proposed different security controls and products that can help the organization stay protected. I made a report explaining the Return on Investment (ROI) calculation: (Revenue - Cost) = Profit. I further broke it down to Annual Loss Expectancy (ALE), Annualized Rate of Occurrence (ARO), and Single Loss Expectancy (SLE).
ALE = ARO x SLE.
My report explains that cybersecurity is an investment that does not produce revenue but prevents money from being spent on incidents. Therefore, the saved money would be considered as the revenue in the formula. Being confident in what I learned in this course, I was able to have the organization purchase an Uninterruptable Power Supply (UPS) for multiple critical systems. The UPS will save the organization time and money by not having to restart their work and have time to offload or keep work that has been done. The knowledge I learned during the course I could immediately implement to my job and teach others the importance of a DRP and ISSP.